What is a Cloud Security Assessment Checklist?
A cloud security assessment checklist is a structured framework used to evaluate the security posture, compliance readiness, and risk exposure of cloud environments. It helps organizations validate whether critical safeguards, such as access controls, encryption, configuration baselines, and monitoring systems, are properly implemented and aligned with industry standards like HIPAA, ISO 27001, and SOC 2.
This checklist covers essential domains, including Identity and Access Management (IAM), data security, network segmentation, system hardening, governance controls, and disaster recovery. It supports visibility through tools like Cloud Security Posture Management (CSPM) and SIEM, while emphasizing proactive strategies such as role-based access control (RBAC), multi-factor authentication (MFA), encryption protocols (e.g., AES-256), and incident response planning. By following this checklist, organizations can identify misconfigurations, reduce vulnerabilities, and maintain continuous compliance across multi-cloud environments.
Why is a Cloud Security Assessment Checklist Important?
A cloud security assessment checklist offers a consistent, repeatable method to evaluate the effectiveness of your cloud controls, uncover risks, and verify compliance with security standards. It ensures that all critical areas, from IAM and encryption to monitoring and recovery, are systematically reviewed, reducing blind spots and supporting better decision-making.
Here are some key reasons why a cloud security assessment checklist is important.
- Ensures consistent evaluation across all cloud accounts and services
- Identifies security gaps and misconfigurations early
- Supports regulatory compliance and audit readiness (e.g., SOC 2, HIPAA)
- Enhances visibility into access, data flow, and control enforcement
- Prioritizes risk mitigation based on system criticality
- Enables continuous improvement through structured monitoring and remediation
- Aligns IT, security, and compliance teams on shared security objectives
- Reduces the likelihood of data breaches or unauthorized access incidents
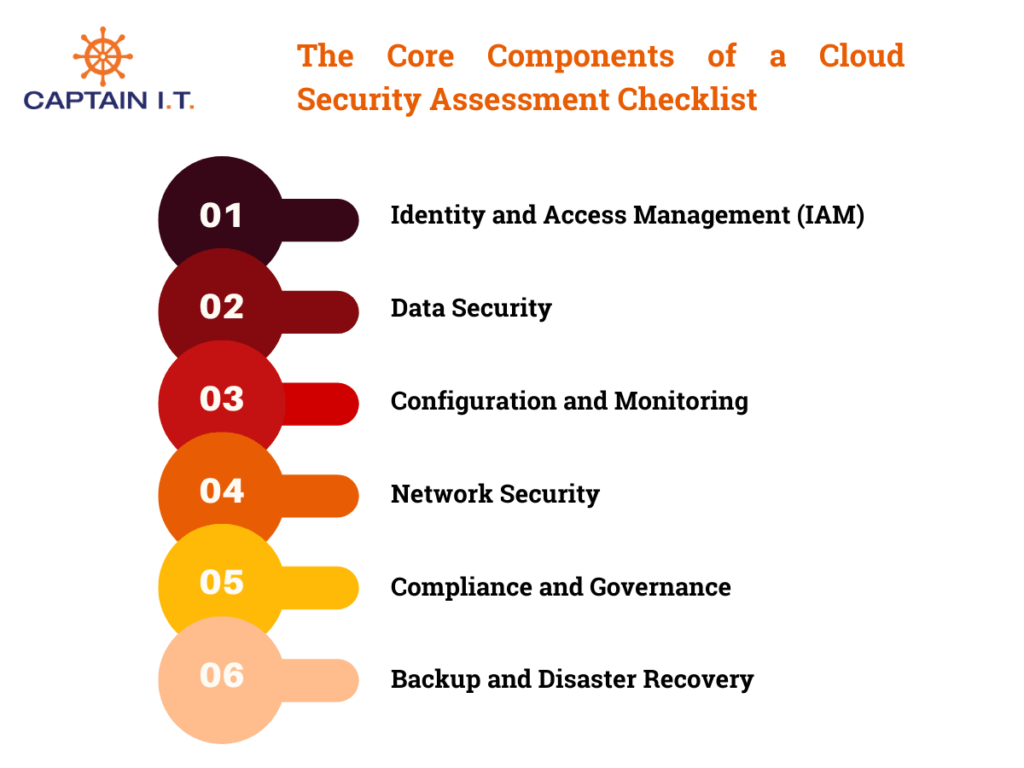
What Are The Core Components of a Cloud Security Assessment Checklist?
The key components of a cloud security assessment checklist include: defining scope, gathering information, risk assessment, reviewing security controls, IAM, data security, network security, configuration monitoring, compliance, incident management, and remediation planning. These elements collectively ensure that your cloud environment is secure, compliant, and audit-ready. Each component addresses a different layer of protection, ranging from access governance and threat detection to encryption and recovery, to help organizations reduce risk, enforce controls, and maintain continuous oversight in dynamic cloud ecosystems.
Define Scope and Objectives
Scoping sets the boundaries for your assessment, ensuring focus on the right assets, users, and compliance requirements. Without clear objectives, assessments may miss critical risks or waste effort on irrelevant areas. Establishing a defined scope also aligns teams around audit readiness, cloud governance, and security baselines tailored to your environment.
- Identify cloud providers, accounts, services, and environments (prod, dev)
- Define goals: risk reduction, compliance verification, security hardening
- Map dependencies across applications and workloads
- Outline applicable regulatory frameworks (e.g., SOC 2, HIPAA, CMMC)
Gather Cloud Environment Information
An accurate cloud audit starts with complete visibility. Gathering logs, configurations, and identity mappings provides the forensic depth required to analyze exposure, trace risk propagation, and benchmark compliance. This foundational step supports ongoing monitoring, threat detection, and data classification by aggregating relevant telemetry into one cohesive view.
- Collect cloud logs (API calls, auth events, access history)
- Export infrastructure and IaC configuration files
- Retrieve IAM role and policy relationships
- Centralize findings into a SIEM, data lake, or analysis platform
Conduct Risk Assessment
Risk assessments help security teams focus on what matters most. By evaluating the probability and impact of threats, such as misconfigurations, access violations, or data exfiltration, you can prioritize controls that reduce business risk. This process supports budget allocation, compliance posture, and mitigation planning.
- Score vulnerabilities using likelihood-impact risk matrices
- Identify critical cloud resources exposed to public access
- Assess third-party integration risks and compliance exposure
- Analyze data sensitivity in exposed services (e.g., S3, Azure Blob)
Review Security Controls
Effective cloud security depends on functional, monitored controls. This review ensures that technical defenses, like firewalls, intrusion detection, and encryption, are properly configured and aligned with both internal policies and external standards. Regular control validation reduces the chance of silent failure or shadow infrastructure.
- Audit network security groups, ACLs, and firewall rules
- Validate encryption configuration for data at rest and in transit
- Confirm identity controls: MFA, RBAC, privileged access separation
- Inspect DLP systems, intrusion detection tools, and audit log integrity
Identity and Access Management (IAM)
IAM defines how users access cloud resources and what level of control they have. Without clear boundaries, excessive permissions can lead to insider threats or unauthorized external access. Strengthening IAM ensures that access is both intentional and minimal, aligned with operational needs. To secure identity controls effectively, organizations should follow these key actions:
- Implement role-based access control (RBAC)
- Use multi-factor authentication (MFA) for all user accounts
- Review inactive or orphaned accounts regularly
- Configure conditional access and Just-in-Time (JIT) elevation policies
- Limit the use of global/admin privileges
Data Security
Safeguarding data is critical to protecting business operations and meeting regulatory requirements. Effective data security not only encrypts sensitive files but also classifies and restricts them based on access needs. By tagging and isolating critical information, organizations reduce the risk of accidental exposure or intentional theft. To build a defensible data security posture, the following practices should be consistently applied:
- Encrypt data using TLS in transit and AES-256 at rest
- Classify data by sensitivity: public, internal, confidential, restricted
- Apply DLP policies to control data egress
- Enable secure file sharing policies
- Manage encryption keys in cloud-native or external KMS solutions
Network Security
Cloud networks require boundary enforcement, segmentation, and traffic inspection to prevent unauthorized access or lateral movement. A robust network security strategy limits exposure, enforces isolation between workloads, and supports real-time detection of anomalous traffic patterns.
- Segment workloads using VPCs, VNETs, and subnets
- Apply ingress/egress rules to security groups and firewalls
- Eliminate unused or exposed public IP endpoints
- Deploy IDS/IPS solutions for traffic inspection and alerting
- Use private service endpoints and encrypted interconnects
Configuration and Continuous Monitoring
Maintaining consistent and secure configurations across cloud services is essential for reducing attack surfaces. Continuous monitoring enables teams to identify unauthorized changes and respond promptly to emerging threats. To manage configuration integrity and visibility, organizations should implement the following controls:
- Define configuration baselines aligned with benchmarks (e.g., CIS)
- Use CSPM tools to detect misconfigurations across cloud services
- Enable real-time alerts on access or configuration changes
- Review logs and metrics for abnormal user or system behavior
- Schedule automated posture reviews and drift scans
Compliance and Regulatory Alignment
Maintaining compliance means mapping cloud controls to the requirements of industry standards and laws. This includes documenting practices, validating encryption and access policies, and ensuring all third-party vendors also meet compliance expectations. Gaps here can lead to penalties or reputational damage.
- Align cloud operations with HIPAA, PCI-DSS, ISO 27001, etc.
- Define data retention, sovereignty, and residency policies
- Maintain asset inventories and access/audit logs
- Review third-party certifications and service-level agreements (SLAs)
- Perform internal compliance audits and readiness reviews
Backup and Disaster Recovery
A resilient cloud strategy includes preparing for data loss, outages, or attacks. Effective backup and recovery procedures reduce downtime and ensure operational continuity. To secure recovery capabilities and protect business-critical data, apply these proven practices:
- Verify that cloud backup policies are in place and automated
- Test restore procedures regularly
- Ensure snapshots and backups are protected from deletion
- Define RTO and RPO for cloud workloads
- Use geo-redundant backup strategies for critical data
Incident Management
Preparedness determines response success. A documented, role-specific incident plan supports rapid triage, legal response, and forensic review. Testing and automation make your team faster and more coordinated during high-stress events.
- Define roles and response phases (detect, contain, recover)
- Build escalation paths and contact trees
- Integrate detection tools with SOAR or ticketing systems
- Conduct simulations and update playbooks annually
- Store evidence logs securely for post-incident analysis
Remediation Planning
Once issues are detected, organizations must act quickly and smartly. Remediation planning ensures vulnerabilities are resolved in order of business impact, resources are used effectively, and decisions are tracked for accountability and governance.
- Prioritize remediations using CVSS and business context
- Focus on internet-exposed, privileged, or compliance-relevant flaws
- Assign owners and due dates via dashboards or workflows
- Track mitigated vs deferred issues for compliance audits
- Include compensating controls where patching isn’t feasible
What Are The Best Practices for Cloud Security Assessment?
The best practices for cloud security assessment focus on improving visibility, accountability, and response across your cloud environment. These include using automated tools like CSPM and SIEM for monitoring, maintaining an incident response plan, prioritizing patching based on risk, regularly reviewing the shared responsibility model, and enforcing least privilege and Just-in-Time access. Together, these practices help organizations detect vulnerabilities early, respond effectively to threats, and maintain continuous alignment with security and compliance goals.
Use CSPM and SIEM Tools
Monitoring and visibility are essential components of any successful cloud security strategy. Cloud Security Posture Management (CSPM) tools help identify misconfigurations across cloud services, while Security Information and Event Management (SIEM) platforms centralize and analyze security logs. When combined, they provide a clear view of system health and help enforce compliance standards. To establish an effective cloud monitoring framework, organizations should take the following steps:
- Deploy CSPM tools to scan for policy violations and misconfigurations
- Integrate SIEM platforms to collect, normalize, and analyze security logs
- Correlate events across services to detect anomalies or advanced threats
- Use dashboards and alerts for real-time response to critical issues
- Align CSPM and SIEM use with regulatory reporting and audit needs
Establish a Cloud Incident Response Plan
Every cloud environment should have a defined plan to respond to security incidents quickly and effectively. A clear incident response plan minimizes disruption and supports legal and audit readiness. It should outline who does what and when across all phases of a security event. To build and maintain an effective plan:
- Define response phases, including detection, containment, and recovery
- Assign roles and responsibilities to internal response teams
- Conduct tabletop exercises to test workflows and decision-making
- Document communication procedures for internal and external parties
- Align your plan with standards such as NIST SP 800-61
Prioritize Patching Based on Risk
Not all vulnerabilities present the same level of threat, which makes prioritization essential in any patch management strategy. A risk-based approach allows teams to focus on high-impact exposures, such as those affecting internet-facing systems or critical workloads, while deferring less urgent updates. This ensures resources are used efficiently, minimizes operational disruption, and strengthens overall cloud security posture. To improve patch management efficiency:
- Use CVSS scores and asset criticality to prioritize patches
- Identify internet-facing and high-value assets first
- Apply automated tools for vulnerability scanning and classification
- Track patch progress through dashboards or ticketing systems
- Schedule regular patching windows for high-risk components
Review the Shared Responsibility Model Regularly
Security in the cloud is shared between provider and customer, but the division of responsibilities changes depending on the service model. Misunderstanding these boundaries can lead to unprotected assets or gaps in control. Regularly reviewing the shared responsibility model ensures clear ownership and accountability. To maintain clarity and control:
- Review provider documentation for IaaS, PaaS, and SaaS models
- Identify which controls fall under customer responsibility
- Adjust internal policies based on any provider-side updates
- Validate encryption, access, and patching responsibilities regularly
- Educate teams to avoid reliance on provider coverage in key areas
Enforce Least Privilege and JIT Access
Over-permissioned accounts increase the risk of misuse, especially in complex cloud environments. Enforcing least privilege ensures users only access what they need, while Just-in-Time (JIT) access limits exposure to short, approved timeframes. Together, these practices reduce attack surface and insider risk. To strengthen access control:
- Audit roles and remove unnecessary permissions
- Set up time-bound JIT access for sensitive resources
- Use tools like Azure AD PIM or AWS IAM Access Analyzer
- Implement access review workflows to catch drift
- Monitor administrative activity closely for signs of misuse
Secure Your Cloud with a Trusted Partner
Managing cloud security effectively requires more than internal resources and occasional audits. It takes consistent oversight, technical expertise, and real-time response, all of which can be challenging for growing teams. That’s why mid-sized businesses across Southern California and Los Angeles turn to Captain IT, a reliable managed service provider with a proven record in securing complex cloud environments. We deliver hands-on support and structured frameworks to strengthen security posture, ensure compliance, and reduce risk.
From enforcing IAM policies and deploying advanced monitoring tools to managing audits and recovery plans, Captain IT provides end-to-end cloud security services tailored to your environment. Our approach ensures your systems remain secure, your data stays protected, and your operations meet industry and regulatory standards.