Cyberattacks are deliberate and malicious attempts to compromise digital systems, networks, or data by exploiting technical vulnerabilities, human behavior, or trusted relationships. They take many forms, including malware infections, phishing and social engineering, ransomware, denial-of-service attacks, man-in-the-middle interception, injection attacks, credential abuse, and supply chain compromises, each designed to gain unauthorized access, disrupt operations, increase downtime, or steal sensitive information.
Across these attack types, cybercriminals follow a structured process that typically starts with reconnaissance and progresses through delivery, exploitation, system compromise, and execution of objectives such as data theft, financial extortion, or service disruption. These cyberattacks are carried out by a range of actors, including organized cybercriminal groups, nation-state actors, hacktivists, and inexperienced attackers. They target high-value assets such as financial data, personally identifiable information, intellectual property, cloud environments, IoT devices, and critical infrastructure. As digital environments grow more interconnected and attackers adopt automation and artificial intelligence, cyber attacks continue to increase in scale, sophistication, and impact on organizations and individuals alike.
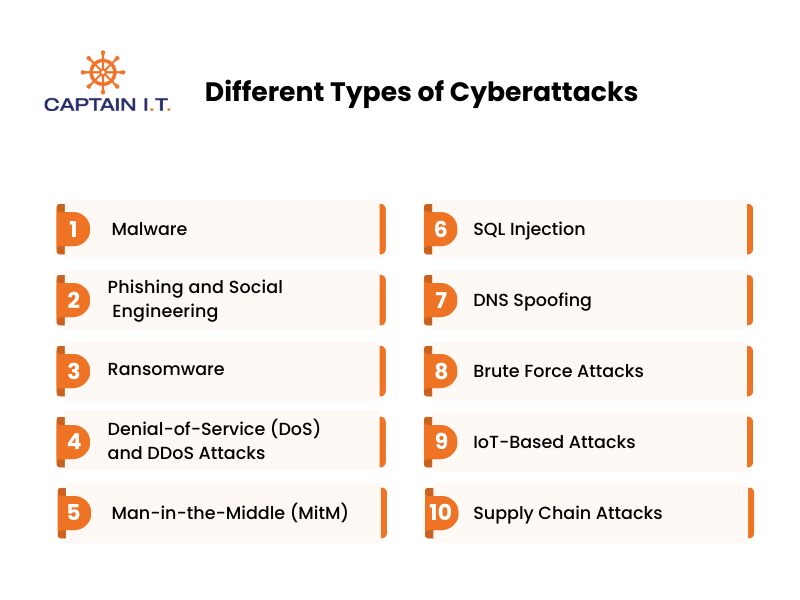
What Are the Different Types of Cyberattacks?
Cyberattacks take many forms, including malware, phishing, ransomware, distributed denial-of-service (DDoS), and man-in-the-middle (MitM) attacks, each designed to exploit specific vulnerabilities in software, networks, and digital systems. Understanding these cyberattack types helps explain how they occur, how attackers operate, and the impact each method can have on data, systems, and business operations, particularly for small and medium-sized businesses (SMBs).
10 different types of cyberattacks include:
- Malware
- Phishing and Social Engineering
- Ransomware
- Denial-of-Service (DoS) and DDoS Attacks
- Man-in-the-Middle (MitM)
- SQL Injection
- DNS Spoofing
- Brute Force Attacks
- IoT-Based Attacks
- Supply Chain Attacks
Malware
A malware attack, also known as malicious software, is a cyberattack that uses malware such as viruses, worms, trojans, and spyware to damage systems, disrupt operations, or gain unauthorized access. Attackers typically spread malware through infected files, compromised websites, phishing emails, or security vulnerabilities such as inactive firewalls or outdated antivirus software.
Once installed, malware spreads across digital systems, compromises software, and gains unauthorized access to data or network resources. Malware disrupts operations, steals sensitive data, weakens security controls, and can cause financial loss, as some malware variants are also used in ransomware attacks. As malware evolves, it becomes more sophisticated, making detection and defense with traditional security measures more difficult.
Phishing and Social Engineering
Phishing, a form of social engineering, is a manipulation technique used by cybercriminals to deceive individuals into disclosing sensitive information such as passwords, banking details, or login credentials. In this cyberattack, attackers impersonate legitimate organizations, such as banks, service providers, or customer support teams, to trick victims into sharing personal or financial information for fraudulent purposes.
Common phishing and social engineering methods include email phishing, smishing (SMS-based attacks), vishing (voice-based scams), baiting, and whaling. These attacks exploit human trust by creating a sense of urgency, fear, or authority, pressuring individuals to respond without verifying the legitimacy of the request. Because phishing targets human behavior rather than technical flaws, it remains difficult to prevent. This has made phishing one of the most frequently reported cybercrimes in the US, with 193,407 individuals reported as victims in 2024 alone, according to Statista.
Ransomware
Part of a malicious cyberattack, ransomware is an extortion-based attack that encrypts a victim’s data or locks users out of systems, then demands a ransom to restore access. It operates as a specialized form of malicious software and is commonly distributed through phishing emails, malicious downloads, remote desktop protocol (RDP) vulnerabilities, or malvertising campaigns. Once deployed, ransomware disrupts normal system operations and places critical data under the attacker’s control, as demonstrated by the 2023 Clop ransomware attack, which exploited a zero-day vulnerability in MOVEit Transfer to exfiltrate sensitive data.
Common ransomware variants include crypto-ransomware (encrypting files), lockers (locking systems), and double extortion (stealing and locking data). These attacks cause financial losses, operational disruptions, and long-term data-availability issues, especially when backups are compromised. Ransomware frequently targets large organizations, government agencies, and critical infrastructure, as seen in the MOVEit incident, which affected over 255 organizations and exposed data on millions of users. Even so, paying the ransom does not guarantee data recovery, leaving many victims with limited options.
Denial-of-Service (DoS) and DDoS Attacks
Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) attacks flood servers, systems, or networks with overwhelming traffic, making services unavailable to legitimate users. DoS attacks originate from a single source using methods such as buffer overflow, ping of death, and flooding. Whereas DDoS attacks use botnets made up of compromised internet-connected devices to generate massive, harder-to-block traffic volumes, often causing severe financial and operational damage.
DDoS attacks are more difficult to mitigate and are commonly observed at traffic levels of 20 to 40 Gbps or higher, sufficient to disrupt or shut down infrastructure. These attacks typically fall into volumetric attacks that consume bandwidth, protocol attacks that exhaust server resources, and application-layer attacks that target services such as HTTP. Common examples of DoS and DDoS attacks include SYN floods, UDP reflection, and yo-yo attacks designed to exploit auto-scaling infrastructure.
Man-in-the-Middle (MitM)
A Man-in-the-Middle (MitM) attack is a cyberattack in which an attacker secretly intercepts communication between two parties, such as a user and a server, who believe they are directly connected. These attacks commonly occur over unencrypted or poorly secured communication channels, including public Wi-Fi networks, where attackers can eavesdrop on data transmissions.
By positioning themselves between the communicating parties, attackers can capture sensitive information such as login credentials, banking details, or private messages, or inject malicious content into the communication stream. MitM attacks take several forms, including active eavesdropping, session hijacking, IP, ARP, or DNS spoofing, and HTTPS or SSL stripping. Each technique allows attackers to redirect, monitor, or manipulate network traffic without user awareness, often leading to credential theft, data exposure, and compromised communication integrity.
SQL Injection
Also known as SQLi, an SQL injection attack is a prevalent and dangerous cyberattack that targets databases by exploiting vulnerabilities in web applications that improperly handle user input. This cyberattack occurs when an attacker inserts malicious SQL code into input fields such as login forms, search boxes, or URL parameters, which the application executes as part of a database query due to insecure coding practices and insufficient input validation.
Once successfully executed, SQL injection allows attackers to bypass authentication controls and gain unauthorized access to backend databases. Attackers can then view, modify, or delete sensitive data, including user credentials, financial records, or personal information. In more severe cases, SQL injection enables privilege escalation, disrupts application functionality, and compromises connected systems, leaving web applications and data integrity highly vulnerable when protections are misconfigured or absent.
DNS Spoofing
DNS spoofing, also known as DNS cache poisoning, is a malicious cyberattack that manipulates Domain Name System (DNS) records to redirect users from legitimate websites to fraudulent, attacker-controlled sites. Attackers corrupt a DNS server’s cache or intercept DNS queries so that domain name requests resolve to malicious IP addresses instead of the correct destination.
When users are redirected to these fraudulent sites, they may unknowingly submit credentials, install malware, or interact with phishing pages that appear to be legitimate websites. Because the attack occurs at the DNS level, it undermines trust in network services and makes detection difficult for users, often leading to credential theft, malware infection, and further network compromise.
Brute Force Attacks
Compared to other forms of cyberattack, a brute force attack relies on persistence rather than advanced exploitation, using automated tools to guess passwords, encryption keys, or PINs until unauthorized access is achieved. This method targets authentication mechanisms and relies on computational power rather than exploiting software vulnerabilities. Weak, short, or reused passwords significantly increase the likelihood of compromise, allowing attackers to access accounts and sensitive systems or data.
Different techniques are used for guessing where simple brute-force attempts test every possible character combination, while dictionary attacks rely on predefined lists of common passwords and phrases. Credential stuffing applies stolen login credentials across multiple platforms, exploiting password reuse. Reverse brute-force tests a single common password against many accounts, while hybrid attacks combine dictionary words with character variations. Password spraying further reduces detection by testing a small set of common passwords across many accounts.
IoT-Based Attacks
IoT-based attacks exploit vulnerabilities in Internet of Things devices, including smart home systems, industrial sensors, routers, and medical equipment. Attackers target these devices to steal data, disrupt services, or use them as entry points into broader networks. Poor security configurations, weak or default credentials, and unpatched firmware make IoT devices especially vulnerable to compromise. In fact, according to IBM X-Force Threat Intelligence, more than 50% of IoT devices have critical vulnerabilities that attackers can exploit, and one in three data breaches now involves an IoT device, highlighting the widespread risk posed by insecure connected systems.
Once compromised, IoT devices are often integrated into botnets to launch large-scale cyberattacks, including DDoS attacks, malware distribution, ransomware deployment, and man-in-the-middle (MitM) attacks. Unencrypted communications and outdated firmware further increase exposure, expanding the attack surface and weakening overall network security across connected environments.
Supply Chain Attacks
A supply chain attacks exploit trusted third-party vendors, service providers, or software dependencies to gain indirect access to an organization’s systems, data, or network. Instead of targeting the primary organization directly, attackers compromise a less-secure supplier or partner, allowing malicious activity to propagate downstream. Common forms include software supply chain attacks, hardware tampering, and attacks against third-party service providers with privileged access.
In many cases, attackers insert malicious code into legitimate software updates, compromise vendor infrastructure, or exploit weak security practices within third-party environments. Because these attacks abuse established trust relationships, they often bypass traditional security controls and remain undetected for extended periods. As a result, a single compromised supplier can impact multiple organizations simultaneously, making third-party risk assessment and vendor security management critical for reducing exposure.
How Do Cyber Attack Occurs?
A cyberattack occurs through a structured sequence of actions that begins with information gathering and progresses through tool development, attack delivery, system breach, installation, and execution. Actors (criminals, nation-states, or insiders) use a combination of technical tools, exploitation techniques, and deceptive methods to identify vulnerabilities, gain unauthorized access, and maintain control over targeted systems. Each stage builds on the previous one, allowing attackers to move deeper into networks or applications while minimizing detection and increasing the attack’s overall impact.
6 common phases of how a cyber attack occurs:
- Reconnaissance and Information Gathering
The cyberattack process begins with reconnaissance, during which attackers research and gather information about the target. This includes identifying weaknesses, such as identifying IP addresses, domain names, exposed services, employee details, and system configurations. Attackers use scanning tools, open-source intelligence, and social media analysis to map potential entry points. This step allows attackers to understand the target environment and identify exploitable vulnerabilities. - Weaponization and Tool Development
After gathering information, attackers prepare malicious tools (malware) tailored to the target. This step involves creating malware, exploit kits, phishing emails, or malicious scripts that exploit identified weaknesses. Attackers may customize existing tools or develop new ones to bypass security controls and increase the likelihood of success. - Delivery of the Attack
During the delivery phase, attackers transmit the malicious payload to the target using various methods, including phishing emails, malicious links, infected attachments, compromised websites, and supply-chain vectors. The goal of this step is to place the attack tool into the target environment without triggering security alerts. - Exploitation and Initial Breach
Exploitation occurs when the delivered payload exploits a vulnerability to execute malicious code. This may involve exploiting software flaws, weak credentials, or misconfigured systems. Once successful, attackers gain an initial foothold, allowing unauthorized access to systems or networks. - Installation and System Compromise
After gaining access, attackers install malware, backdoors, or remote access tools to maintain persistence. This step ensures continued control over the compromised digital system even after reboots or credential changes. Attackers may also escalate privileges to gain broader access across the environment. - Execution of Attack Objectives
In the final stage, attackers carry out their intended objectives, such as stealing sensitive data, encrypting files for ransom, disrupting services, or launching additional attacks. Actions taken during this phase directly result in financial loss, data breaches, operational disruption, or reputational damage for the affected organization.
Who Launches Cyber Attacks?
Cyberattacks are launched by a range of threat actors, including organized cybercriminal groups, nation-state actors, hacktivists, and script kiddies. Each group is motivated by different factors such as financial gain, political objectives, ideological causes, or technical curiosity. These attackers also differ in skill level, resources, and operational scale, ranging from highly coordinated criminal networks to individual actors with limited expertise.
Key launchers of cyberattacks include:
- Organized Cybercriminal Groups
These groups are formed around professional attackers who operate as coordinated teams with defined roles such as developers, operators, and money launderers. Their primary motivation is financial gain, and they commonly launch attacks involving ransomware, phishing, fraud, and data theft. These groups target businesses, individuals, and financial institutions to steal sensitive data, demand ransom payments, or conduct large-scale cybercrime operations. - Nation-State Actors (Government-Backed)
Nation-state actors are government-backed groups that conduct cyberattacks to support political, military, or economic objectives. These attackers are highly skilled and well-funded, often engaging in cyber espionage, surveillance, or attacks against critical infrastructure. Their activities may include stealing intellectual property, disrupting national services, or influencing geopolitical outcomes. - Hacktivists
Formed by groups or individuals, hacktivists launch cyberattacks to promote ideological, political, or social causes. Their attacks are often intended to raise awareness, protest organizations, or expose information rather than achieve direct financial gain. Common tactics include website defacement, data leaks, and denial-of-service attacks targeting governments, corporations, or institutions they oppose. - Script kiddies
Script kiddies are inexperienced attackers who rely on pre-built tools, scripts, or exploits created by others. Their motivations often include curiosity, experimentation, or the desire to gain recognition. While they lack advanced skills, their actions can still cause disruption, especially when they exploit known vulnerabilities or target poorly secured systems.
What Are the Common Targets of a Cyber Attack?
Common targets of cyber attacks include financial assets, critical infrastructure such as healthcare and utilities, intellectual property, email systems, and websites. Cybercriminals target these systems because they contain sensitive data, enable financial gain, or allow attackers to disrupt operations and gain unauthorized control.
6 common targets of a cyber attack are:
- Financial Assets and Data
Cybercriminals often target financial assets and related data such as banking systems, payment platforms, and financial records to steal funds, commit fraud, or sell data on illicit markets. Additionally, compromised financial data enables identity theft, unauthorized transactions, and long-term financial loss for organizations and individuals. - Critical Infrastructure
Critical infrastructure includes systems that support essential services such as energy, transportation, healthcare, and utilities. Attackers target these systems to disrupt operations, cause widespread outages, or apply political and economic pressure. Successful attacks can lead to service downtime, public safety risks, and large-scale economic impact. - Personal Identifiable Information (PII)
Sensitive personal data such as names, addresses, identification numbers, and login credentials is a high-value target for cybercriminals. This information enables identity theft, account takeover, and financial fraud when misused. Stolen PII is often traded on illicit markets or reused in future attacks, increasing long-term risk for both individuals and organizations. - Intellectual Property
Intellectual property (IP) includes proprietary research, product designs, trade secrets, and confidential business strategies. Attackers target this data to gain a competitive advantage, support espionage, or sell valuable information to competitors or foreign entities. Loss of intellectual property can weaken innovation and market position. - Email and Communication Systems
Access to internal communication platforms gives attackers visibility into sensitive conversations, credentials, and workflows. By compromising email accounts, attackers can launch phishing campaigns, impersonate trusted users, or intercept confidential information. Control over communication systems often enables lateral movement and facilitates broader attacks across an organization. - Websites and Web Applications
Websites and web applications are common targets because of their exposed interfaces and frequent vulnerabilities. Attackers exploit these systems to steal data, deface content, distribute malware, or disrupt online services. Compromised applications can also serve as entry points into internal networks.
How to Detect a Cyber Attack?
Detecting a cyberattack involves monitoring for unusual network activity, unauthorized access attempts, unexpected system crashes, and disabled security software. These warning signs indicate abnormal behavior within systems or networks that may signal malicious activity. Identifying these indicators early helps organizations and individuals respond quickly, reduce damage, and prevent attackers from gaining deeper access or achieving their objectives.
4 key warning signs to detect a cyber attack include:
- Unusual Network Activity
Abnormal network behavior, such as sudden spikes in outbound traffic, repeated connection attempts to unfamiliar IP addresses, or data transfers outside normal business hours, may signal malicious activity. These patterns often indicate data exfiltration, malware communication, or command-and-control traffic, which can degrade performance and expose sensitive data. - Unauthorized Access Attempts
Repeated failed login attempts, logins from unfamiliar locations, or access to systems outside a user’s normal role can indicate unauthorized access attempts. Attackers often test credentials through brute-force or credential-stuffing attacks before gaining entry. Monitoring authentication logs helps identify account compromise and prevents escalation into deeper system access. - Unexpected System Crashes or Performance Issues
Frequent system crashes, unexplained slowdowns, or applications failing without a clear cause can signal malware execution or resource abuse. These issues may result from malicious processes consuming system resources, corrupted files, or unauthorized software running in the background, often disrupting normal operations. - Disabled Security Software
Security tools being unexpectedly disabled or altered are a strong indicator of an active cyberattack, as attackers often disable antivirus software, firewalls, or intrusion detection systems to avoid detection. Sudden changes in security configurations should be treated as high-risk events requiring immediate investigation.
What Are the Impacts of Cyberattacks on Organizations and Individuals?
Cyberattacks have a wide range of consequences for organizations and individuals, including financial losses, data breaches, reputational damage, operational disruptions, and legal penalties. The impact often extends beyond the initial attack, creating long-term challenges related to recovery, trust, and compliance. SMBs are particularly more vulnerable to cyberattacks, with the National Cyber Security Alliance even indicating 60% of small companies go out of business within six months of a significant cyberattack due to the overwhelming recovery costs
5 major impacts of cyberattacks on organizations and individuals are:
- Financial Losses
In the wake of cyberattacks, organizations are likely to incur high costs for ransom payments, fraud, system restoration, incident response, and business downtime. Individuals may suffer from unauthorized transactions, drained accounts, or identity-related financial fraud, resulting in both short-term and long-term financial losses. This makes direct financial loss one of the most immediate impacts of a cyberattack. - Data Breaches
A data breach occurs when sensitive information is accessed or stolen without authorization, exposing private data to misuse. These incidents often involve customer records, login credentials, and financial information, increasing the risk of identity theft and fraud. The threat remains significant, as customer personal identifiable information (PII) accounted for 53% of all compromised data in 2025, according to IBM. - Reputational Damage
Loss of trust, especially for SMBs, is a significant consequence following a cyberattack. Organizations that experience breaches may suffer reputational damage, leading to reduced customer confidence, client losses, and long-term brand harm. In fact, according to Qualysec, 29% of SMBs that suffer a data breach permanently lose customers. Furthermore, reputational damage can persist even after systems are restored, affecting business relationships and market credibility. - Operational Disruption
Cyberattacks can disrupt daily operations by disabling systems, shutting down services, or corrupting critical data. These disruptions may halt production, delay services, or interrupt essential business processes. For individuals, compromised devices or accounts can prevent access to personal data and online services. - Legal Penalties
In today’s strict regulatory environment, a cyberattack or data breach is often followed by regulatory investigations and financial penalties. Organizations that fail to protect customer information may face fines for non-compliance with data protection laws such as the GDPR or the CCPA. These penalties can be substantial, with fines reaching up to 4% of a company’s global annual turnover, adding significant financial and legal pressure during the recovery process.
What Are the Preventive Tips to Defend Against Cyber Attacks?
Defending against cyber attacks requires a proactive approach that includes using strong passwords, updating software, maintaining security software, backing up data, and monitoring network activity. These measures reduce exposure to common attack methods by strengthening access controls, closing security gaps, and enabling early threat detection. Such practices are widely recognized as effective cybersecurity tips for small businesses and larger organizations, helping limit unauthorized access, data loss, and operational disruption when consistently applied.
6 essential preventive tips to defend against cyber attacks:
- Use Strong Passwords and Multi-Factor Authentication:
Strong passwords and multi-factor authentication (MFA) protect accounts by requiring more than just a username and password. This approach includes long passwords that mix letters, numbers, and symbols, such as T9#rQ!m4L@82, along with an additional verification factor, such as a one-time code or biometric check. MFA significantly reduces the risk of account compromise from phishing, brute-force, and credential-stuffing attacks. - Keep Software and Systems Updated:
Regular software and system updates ensure operating systems, applications, and devices are protected against known vulnerabilities. Software updates patch security flaws that attackers commonly exploit, reducing exposure to malware, ransomware, and zero-day attacks that can arise from outdated systems. - Install and Maintain Security Software:
Security software, such as antivirus, firewalls, and intrusion detection tools, helps identify and block malicious activity. Keeping these tools properly configured and up to date improves real-time threat detection and prevents unauthorized access or malware execution. - Implement Regular Data Backups:
Regular backups protect against ransomware, system failures, or accidental deletion. Secure, offline, or cloud-based backups allow systems to be restored quickly without paying ransoms or suffering permanent data loss. - Conduct Employee Security Training:
Educating employees helps them recognize phishing attempts, social engineering tactics, and unsafe online behavior. Well-trained users are less likely to click on malicious links, share credentials, or unknowingly enable cyberattacks, reducing the risk of human-related security incidents. - Monitor Network Activity:
Continuous network monitoring helps detect unusual traffic patterns, unauthorized access attempts, and suspicious behavior. Early detection allows faster response, limiting damage and preventing attackers from moving deeper into systems.
What Are the Essential Measures for Cyberattack Response and Recovery?
Essential measures for cyberattack response and recovery include isolating affected systems, assessing damage, notifying teams, eliminating threats, restoring backups, and strengthening security controls. Acting quickly and in the correct sequence helps contain the incident, minimize operational disruption, ensure systems are restored securely, and reduce the risk of repeat attacks.
Here are the essential measures of cyberattack response and recovery:
- Isolate Affected Systems:
Isolating affected systems involves disconnecting compromised devices, servers, or networks from the rest of the environment. This step prevents attackers from spreading laterally, limits data exfiltration, and preserves evidence for investigation. Isolation also helps contain the attack while recovery actions are planned and executed. - Assess the Damage and Scope:
Conduct a damage assessment to determine which systems, data, and users are affected by the attack. Security teams analyze logs, alerts, and system behavior to identify the attack type, entry point, and extent of compromise. Understanding the full scope helps guide recovery decisions and prevent reinfection. - Notify Relevant Authorities and Stakeholders:
Timely notification ensures compliance with legal, regulatory, and operational obligations. Organizations may need to inform regulators, law enforcement, customers, and internal stakeholders depending on the nature of the breach. Clear communication helps manage risk, maintain transparency, and support coordinated response efforts. - Contain and Eliminate the Threat:
Containment focuses on stopping malicious activity, while elimination removes malware, backdoors, or unauthorized access. This may involve patching vulnerabilities, resetting credentials, and removing malicious files. Proper containment prevents attackers from regaining access during recovery. - Restore Systems from Secure Backups:
System restoration uses clean, verified backups to recover data and services without reintroducing threats. Secure backups enable faster recovery from ransomware, system corruption, or data loss and reduce reliance on ransom payments or incomplete repairs. - Strengthen Security Controls:
After recovery, security controls must be reinforced to address gaps exploited during the attack. This includes updating systems, improving access controls, enhancing monitoring, and enforcing stronger authentication. Strengthening defenses reduces the likelihood of repeat incidents. - Collaborate with Trusted Cybersecurity Providers:
Working with experienced Managed Security Service Providers (MSSPs) supports effective incident response, forensic analysis, and long-term risk reduction. External specialists provide expertise, tools, and guidance that help organizations recover more quickly and improve their overall security posture after an attack.
What Are the Latest Trends and Emerging Threats in Cyberattacks?
Cyberattacks continue to evolve as attackers adopt artificial intelligence, automate attack processes, expand ransomware operations through Ransomware-as-a-Service (RaaS), exploit supply chain relationships, and target cloud security vulnerabilities. These emerging trends reflect how cybercriminals are scaling attacks, reducing technical barriers, and focusing on modern, interconnected digital environments.
- AI-Powered and Automated Attacks:
With the growing use of AI across different fields, cyberattackers are using machine learning (ML) to create polymorphic malware that constantly alters its code to evade traditional detection methods. AI is also used to generate highly realistic, targeted phishing messages that adapt to user behavior and context, increasing success rates. As a result, AI-driven attacks have surged sharply, with some sectors reporting increases of more than 1,000%, reflecting a shift toward faster, scalable, and adaptive attack techniques. - Ransomware-as-a-Service (RaaS)
Ransomware has evolved into a service-based model that allows attackers with minimal technical skills to launch sophisticated campaigns. Ransomware-as-a-Service platforms provide ready-made tools, infrastructure, and payment systems in exchange for a share of profits. This model has expanded the scale and frequency of ransomware attacks, which increasingly target critical infrastructure and small- to medium-sized businesses that often lack the resources to recover quickly. - Supply Chain Compromises
Trust relationships between organizations and their vendors have become a primary attack vector for cybercriminals. By exploiting weaker security practices within suppliers, service providers, or software dependencies, attackers gain indirect access to larger targets. A single compromised vendor can affect multiple downstream organizations simultaneously, as seen in recent disruptions to food and logistics supply chains. These attacks are difficult to detect because they bypass traditional perimeter defenses. - Cloud Security Vulnerabilities
The rapid adoption of cloud services has introduced new security risks that attackers actively exploit. Misconfigured cloud environments, insecure APIs, excessive permissions, and stolen credentials provide attackers with direct access to sensitive data and resources. These weaknesses have contributed to a reported 75% increase in cloud-based breaches, enabling large-scale data exposure. As reliance on the cloud grows, proper configuration management and access control enforcement remain critical. - IoT and Smart Device Exploits
The growing number of IoT and smart devices has expanded the attack surface for cybercriminals. Weak security settings, outdated firmware, and unencrypted communications allow attackers to compromise devices and use them to steal data, carry out network intrusions, or launch large-scale botnet attacks. These exploits pose increasing risks to both consumer and enterprise environments.