Network security management (NSM) is the systematic process of securing an organization’s network by continuously monitoring, controlling, and protecting systems, data, and users from unauthorized access and cyber threats through coordinated use of security policies, tools, and procedures. It is essential for maintaining business continuity, protecting sensitive data, and ensuring compliance with regulatory standards. It works by integrating security tools such as firewalls, intrusion prevention systems, access control, VPNs, endpoint security, cloud security, and Security Information and Event Management (SIEM) to enable centralized visibility, real-time monitoring, and consistent policy enforcement across the network.
Key capabilities of network security management include preventing unauthorized access, detecting threats in real time, improving visibility, automating compliance, and reducing operational costs. It also supports policy enforcement and compliance through continuous monitoring and auditing. For small and medium-sized businesses (SMBs), these capabilities help simplify security operations, reduce reliance on large IT teams, and protect critical business data with limited resources. Despite challenges such as evolving threats and tool complexity, applying best practices like Zero Trust and centralized management strengthens security posture, while working with a trusted provider ensures long-term protection and stability.
Why Is Network Security Management Important?
Network security management is important for protecting data integrity, confidentiality, and availability by securing network infrastructure against unauthorized access and advanced cyber threats. It enables business continuity by reducing the risk of downtime through continuous network security monitoring and rapid incident response, while also ensuring compliance with regulatory standards and security policies. Without structured network security management, businesses face increased risks of data breaches, financial losses, regulatory penalties, and prolonged operational downtime from unmitigated cyber incidents.
For SMBs, this structured security management ensures that limited IT resources can still protect critical systems and avoid costly disruptions. At the same time, it supports secure operations across complex and hybrid environments, including cloud and on-premises systems, by defending against threats such as ransomware and other malicious network attacks.
How Does Network Security Management Work?
Network security systems work by integrating tools such as firewalls, VPNs, and Endpoint Detection and Response (EDR) into a single automated interface, enabling continuous monitoring, policy enforcement, and rapid threat detection. It continuously monitors, analyzes, and controls network traffic across an organization’s network infrastructure using integrated security management tools and systems.
A layered framework in network security management combines intrusion detection systems (IDS), access control, and endpoint security to create a coordinated defense. Network administrators enforce security policies, while centralized platforms provide visibility into network devices and user activity. As network security management monitoring detects anomalies or malicious behavior, the system generates alerts and initiates incident response actions to contain and mitigate risks, ensuring secure and controlled network operations.
What Are the Types of Network Security Management?
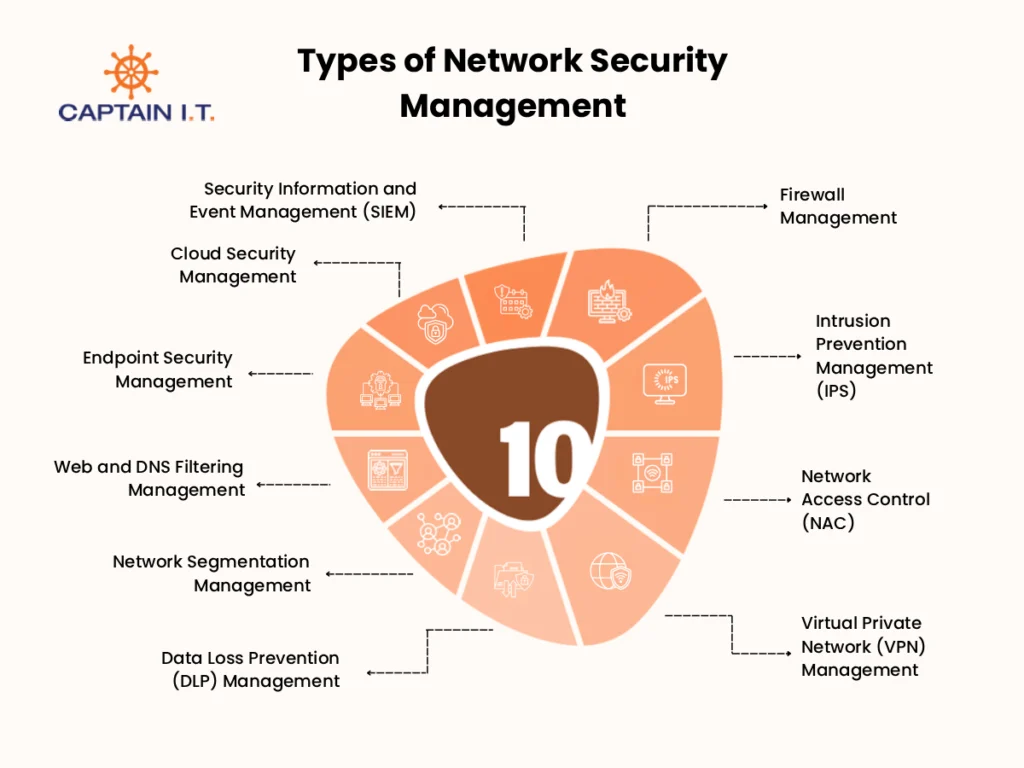
The types of Network Security Management include Firewall Management, Intrusion Prevention System (IPS) Management, Access Control Management (NAC), Virtual Private Network (VPN) Management, and Data Loss Prevention (DLP) Management. Each type addresses a specific layer of network protection, ensuring comprehensive coverage across network infrastructure, user access, data security, and threat detection.
10 types of Network Security Management are:
1. Firewall Management: Controls and filters network traffic.
2. Intrusion Prevention Management (IPS): Detects and blocks cyber threats in real time.
3. Network Access Control (NAC): Restricts network access based on identity.
4. VPN Management: Secures remote connections through encryption.
5. Data Loss Prevention (DLP) Management: Prevents sensitive data leakage.
6. Network Segmentation Management: Isolates network segments to limit threats.
7. Web and DNS Filtering Management: Blocks access to malicious websites.
8. Endpoint Security Management: Protects devices from cyber threats.
9. Cloud Security Management: Secures cloud-based data and applications.
10. SIEM: Monitors and analyzes security events centrally.
- Firewall Management
Firewall management is a core component of network security, involving configuring, monitoring, and maintaining firewalls to control incoming and outgoing network traffic. It works by enforcing security rules that allow or block traffic based on predefined network security policies, helping prevent unauthorized access to the network.
Within the network, firewall management filters malicious traffic, protects network devices, and ensures secure communication between internal systems and external sources such as the internet. It reduces exposure to threats, strengthens access control, and supports a secure, compliant network environment. For SMBs, it provides a cost-effective way to secure limited IT resources, prevent cyberattacks, and maintain stable operations without requiring complex infrastructure. - Intrusion Prevention Management (IPS)
Intrusion Prevention Management (IPS) is a proactive network security control that monitors network traffic in real time, scanning for malicious activity, policy violations, and vulnerabilities. It evaluates traffic patterns, signatures, and behavior to block threats such as malware, exploits, and unauthorized access attempts at the point of detection.
This function limits network vulnerabilities, improves threat response, and maintains continuous protection across systems by stopping attacks before they affect critical network resources. With IPS management, SMBs achieve reduced risk, improved security continuity, and reliable operations without heavy infrastructure investment. - Network Access Control (NAC)
A network security management function that serves as a cybersecurity solution to authenticate, authorize, and enforce security policies on users and devices before and during network access is known as Network Access Control (NAC). It verifies user identities and device compliance before granting access, ensuring only authorized users and endpoints can connect to network resources. NAC monitors endpoints, such as employee laptops and mobile devices, and restricts access if they fail to meet defined security policies.
By controlling network access at every connection point, NAC strengthens overall network protection, enforces security standards, and provides clear visibility into connected devices. NAC allows SMBs to manage access efficiently, enforce policies consistently, and operate without complex administration. - Virtual Private Network (VPN) Management
Virtual Private Network (VPN) Management is a network security management function that enables secure remote access and protects data transmission across public and private networks through encryption. It creates encrypted communication tunnels between users and the network, ensuring data confidentiality and preventing unauthorized interception. VPN management also handles user authentication, controls access, and maintains secure connectivity for remote users and distributed locations.
Through encrypted communication and controlled access, VPN management supports secure network operations and protects sensitive data during transmission. VPN reduces SMBs’ exposure to external threats while ensuring secure access to internal networks and data. - Data Loss Prevention (DLP) Management
Data Loss Prevention (DLP) Management is a strategic network security that monitors, detects, and prevents the unauthorized transfer or exposure of sensitive data across the network. It works by identifying confidential information such as financial records, customer data, or intellectual property, and enforcing security policies to block or restrict its movement outside the organization.
By controlling how data is accessed, shared, and transmitted, DLP management reduces the risk of data breaches, ensures compliance with data protection regulations, and maintains data integrity. It also supports continuous visibility into data usage, allowing businesses to identify risks early and respond to potential threats effectively. - Network Segmentation Management
Network Segmentation Management is a structured security practice that involves dividing a network into smaller, isolated subnetworks to improve security, boost performance, and simplify compliance. It enforces security policies at each segment level, ensuring only approved communication flows between devices, applications, and network zones.
This approach improves visibility into network activity, limits access to critical resources, and reduces the attack surface by containing threats within specific segments. It also helps prioritize protection of high-value assets, such as financial systems and databases. For small and medium-sized businesses (SMBs), network segmentation simplifies network management, strengthens the security posture, and supports stable, secure day-to-day operations. - Web and DNS Filtering Management
A type of network security management that proactively intercepts DNS queries and filters web traffic to block access to malicious, inappropriate, or non-compliant domains before a connection is established is known as Web and DNS Filtering Management. It works by evaluating requested websites against threat intelligence databases, helping prevent access to harmful content and unauthorized web activity across the network.
By filtering DNS queries and controlling access to web domains, Web and DNS Filtering Management reduces exposure to phishing, malware, and ransomware while enforcing safer browsing across the network. It also strengthens policy enforcement by ensuring that all web activity aligns with the business’s security standards and acceptable use policies. - Endpoint Security Management
Endpoint Security Management involves securing and managing endpoint devices, such as laptops, desktops, and mobile devices, to prevent them from becoming entry points for threats. It combines Endpoint Protection Platform (EPP) capabilities with Endpoint Detection and Response (EDR) to prevent, detect, and respond to malware, ransomware, and unauthorized access, especially across hybrid work environments.
This approach strengthens network defense at the device level by enforcing security controls and monitoring endpoint activity, with endpoint security management reducing the risk posed by compromised devices. It also ensures continuous threat visibility and rapid response to endpoint-level incidents, improving overall network security resilience. - Cloud Security Management
Cloud Security Management focuses on securing cloud infrastructure, applications, and data by applying structured policies, access controls, and continuous monitoring across cloud environments. It protects cloud resources by managing user access through least-privilege principles and multifactor authentication (MFA), while also securing data through encryption at rest and in transit, with proper encryption key management.
Continuous monitoring and configuration management within cloud security management help identify misconfigurations, track user activity, and detect threats across platforms such as AWS or Microsoft Azure. This approach strengthens data protection, reduces risks, and supports compliance, while giving SMBs a scalable way to secure cloud operations without complex infrastructure. - Security Information and Event Management (SIEM)
Security Information and Event Management (SIEM) is a network security management solution that collects, analyzes, and correlates security data from multiple sources across the network to detect and respond to threats. It works by aggregating logs and events from network devices, servers, and applications, then analyzing them in real time to identify suspicious activity and potential security incidents.
By providing centralized visibility and real-time threat detection, SIEM improves incident response and helps reduce the impact of security events. For small and medium-sized businesses (SMBs), it offers a structured way to monitor network activity, detect threats early, and maintain stronger security oversight without complex manual processes.
What Are the Benefits of Network Security Management?
The benefits of Network Security Management include preventing unauthorized access, detecting threats in real time, centralizing network visibility, automating compliance, streamlining incident response, and reducing costs. These capabilities are supported by continuous monitoring, proactive threat management, and structured oversight from an MSP to maintain consistent, responsive security operations.
6 key benefits of the network security management include:
- Prevents Unauthorized Access to Your Network
Network security management restricts unauthorized access by applying identity verification, firewall rules, and access control policies across network systems. Only approved users and compliant devices can interact with sensitive resources, reducing exposure to breaches and misuse. This level of protection helps maintain data integrity and operational stability, while also enabling SMBs to safeguard critical business information without relying on complex in-house security setups. - Detects and Neutralizes Threats Instantly
Network security management enables real-time monitoring to identify suspicious activity and stop threats before they spread across the network. By analyzing traffic and triggering automated responses, it blocks malware and intrusion attempts early, with these capabilities often supported by an MSP to maintain consistent security operations. This immediate action reduces downtime and operational disruption, enabling SMBs to maintain continuous operations while protecting systems from rapidly evolving cyber threats. - Centralizes Visibility Across Network Infrastructure
For centralized visibility, network security management aggregates data from devices, endpoints, and applications into a unified platform, providing a complete view of network activity. This visibility enables faster anomaly detection, improved tracking of user activity, and better identification of vulnerabilities. With this level of insight, SMBs can maintain stronger control over their network environment and make informed security decisions without needing large security teams. - Automates Compliance and Reduces Regulatory Risk
Compliance processes become more manageable as network security management automates policy enforcement, monitors activities, and generates audit-ready reports aligned with regulatory standards, often with support from an MSP to maintain consistent oversight. It ensures consistent implementation of security controls across the network, reducing the likelihood of compliance gaps. This approach helps organizations meet regulatory requirements, avoid penalties, and maintain trust with customers and partners. - Streamlines Incident Response and Recovery
Network security management enables faster response to security incidents through automated alerts and predefined response actions, ensuring immediate awareness of potential threats. It supports quick detection, containment, and recovery from attacks, minimizing the overall impact on operations and preventing escalation. This structured response improves resilience, helping SMBs reduce downtime, restore systems efficiently, and maintain business continuity even during unexpected security events. - Reduces Costs With Security Automation
For reducing costs with security automation, network security management automates routine tasks such as monitoring, threat detection, and policy enforcement. It reduces manual workload, minimizes human error, and ensures consistent security operations across the network. This improved efficiency allows better resource utilization, helping SMBs maintain strong security practices, scale operations as needed, and avoid the cost of complex infrastructure or large IT teams.
What Are the Common Challenges in Network Security Management?
The common challenges in network security management include managing ever-evolving cyber threats, a lack of centralized network visibility, the complexity of handling multiple security tools, and maintaining compliance with changing regulations. These challenges make it difficult to maintain consistent security, respond quickly to threats, and ensure effective protection across network infrastructure, often leading organizations to rely on an MSP for continuous monitoring and coordinated security management.
4 common challenges in network security management include:
- Managing Ever-Evolving Cyber Threats
Cyber threats such as ransomware, phishing, malware, and zero-day exploits continue to evolve in complexity and frequency, making consistent protection difficult. Attackers now use AI-driven phishing, automated attack tools, and polymorphic malware that adapts to bypass detection systems. This rapid evolution increases the risk of undetected vulnerabilities and delayed responses, requiring continuous updates to security strategies to defend against emerging, more sophisticated threats. - Lack of Centralized Network Visibility
In network security management, when data is spread across multiple systems, it limits visibility into network traffic, user behavior, and vulnerabilities. This lack of centralized visibility creates gaps in monitoring and control, making it harder to detect suspicious activity. It delays threat detection, reduces response efficiency, and increases the risk that security incidents will go unnoticed and impact business operations. - Complexity of Managing Multiple Security Tools
Managing multiple security tools within network security management often leads to operational complexity and coordination challenges. Each solution runs independently, requiring separate configuration, updates, and monitoring. This disconnected setup increases the risk of misconfigurations, creates inefficiencies, and delays threat response. As a result, maintaining unified security policies across all tools becomes difficult and consumes more time and resources. - Maintaining Compliance With Changing Regulations
Regarding network security management, maintaining compliance is challenging because evolving regulations require continuous updates to security policies, controls, and processes. As standards change, businesses must adapt quickly while ensuring all systems remain aligned and properly documented. This effort increases complexity, requires continuous monitoring and auditing, and strains resources. Failure to keep up raises the risk of non-compliance, penalties, and loss of business credibility.
How Does Network Security Policy and Compliance Management Work?
Network Security Policy and Compliance Management works by defining, implementing, monitoring, and continuously updating security rules to protect network integrity and ensure only authorized traffic is allowed. It uses centralized management tools to automate firewall configurations, analyze network traffic, and audit policy changes, reducing the risk of misconfigurations. These policies align with regulatory standards such as HIPAA, GDPR, and PCI DSS, ensuring compliance while maintaining secure network operations.
Through continuous monitoring and auditing, network security management tracks user activity, detects policy violations, and ensures policies remain enforced and up to date. This structured approach helps organizations maintain compliance, reduce risks, and ensure consistent protection across their network infrastructure.
What Are the Best Practices for Effective Network Security Management?
The best practices for effective network security management include implementing Zero Trust, enforcing access control policies, deploying real-time monitoring, keeping systems up to date, conducting regular audits, and maintaining centralized security management. These practices help ensure consistent protection, reduce security gaps, and strengthen overall network resilience against evolving threats.
- Implement a Zero Trust Security Architecture
For effective network security management, implementing a Zero Trust Architecture ensures no user or device is trusted by default. It enforces continuous identity verification, device validation, and strict access control, supported by network segmentation, least-privilege access, and multi-factor authentication (MFA) to reduce the risk of unauthorized access and strengthen network protection. - Conduct Regular Network Security Audits
Regular network security audits strengthen network security management by identifying vulnerabilities, misconfigurations, and gaps in security controls. This process, often guided by a structured network security checklist, involves reviewing network devices, access policies, and system logs through scheduled assessments and vulnerability scans. It helps ensure security measures remain effective, reduces risk exposure, and maintains a secure and compliant network environment - Enforce Strict Access Control Policies
Effective network security management requires strict access control policies to limit network access to authorized users and verified devices. This is implemented through role-based permissions, identity verification, and continuous access monitoring. By restricting access and enforcing authentication, organizations reduce the risk of unauthorized entry and protect sensitive systems. - Deploy Real-Time Network Monitoring and Threat Detection
Maintaining effective network security management depends on real-time monitoring to identify and respond to threats as they occur. This involves analyzing network traffic, user behavior, and system activity using detection tools and automated alerts. Immediate visibility allows faster response, minimizes potential damage, and ensures continuous protection against evolving cyber threats. - Keep All Network Devices and Software Updated
Up-to-date systems play a critical role in effective network security management by reducing exposure to known vulnerabilities. Regular patching, firmware updates, and automated update processes ensure that security gaps are addressed promptly. Keeping devices and software current helps prevent exploitation and maintain a strong, reliable security posture across the network. - Develop and Test an Incident Response Plan
For effective network security management, developing and testing an incident response plan ensures a structured approach to handling security incidents. It defines steps for detection, containment, and recovery, supported by assigned roles and regular testing. This approach enables faster response, reduces disruption, and maintains business continuity during security events. - Centralize Security Management Across All Network Infrastructure
Maintaining effective network security management requires centralizing security operations to ensure unified control across network systems. It consolidates monitoring, policy enforcement, and threat detection into one platform, improving visibility and coordination. This approach reduces complexity and ensures consistent security practices across the entire network. - Train Employees on Network Security Awareness|
Improving effective network security management requires training employees to recognize threats and follow security practices. It includes education on phishing, safe access, and security policies through regular training. This reduces human error and helps prevent security incidents caused by unsafe user behavior. - Work With a Trusted Network Security Management Provider
When businesses experience downtime due to cyberattacks or struggle with limited IT resources, maintaining consistent network security becomes difficult. Partnering with a trusted Network Security Management provider ensures continuous monitoring, faster threat detection, expert response, and reliable policy enforcement. This support reduces risks, improves stability, and allows businesses to focus on core operations while keeping their network secure and compliant.